Misconception first: many traders treat the sign‑in screen as an innocuous gateway — enter email, password, 2FA, and you’re done. That’s wrong. For active traders in the US, the moment you authenticate is where usability, regulatory friction, and threat models intersect. The mechanics of logging into OKX — whether through the web, mobile app, browser extension, or a non‑custodial wallet — shape what you can do next, what assets are exposed, and what recovery paths exist if things go wrong.
This article walks a realistic case: a US‑based trader who wants to log in, check a futures position, and move some tokens to a self‑custodial wallet. We unpack the technical mechanisms (how OKX validates identity and sessions), the trade‑offs among access paths (web vs. mobile vs. extension vs. non‑custodial), and the operational limits you must accept. Where possible I’ll point to practical heuristics you can reuse the next time you click “okx sign in.”
How OKX sign in works: the mechanism under the hood
At a technical level the OKX sign‑in flow combines three distinct mechanisms: identity proof, device/session management, and continuous risk scoring. Identity proof in the US begins with credentials (email/username + password) and mandatory KYC — a government ID plus liveness check — imposed to satisfy AML rules. Device/session management issues a session token after successful auth and ties it to device fingerprints; tokens are short‑lived for high‑risk actions. Continuous risk scoring uses AI heuristics to flag unusual logins and can force re‑auth or temporary holds.
Two‑Factor Authentication (2FA) is mandatory and supported via SMS, Google Authenticator, or biometrics on mobile. Each 2FA method has a different failure mode: SMS is convenient but vulnerable to SIM swap; TOTP apps are resilient except when you lose the phone or backup codes; biometrics are user‑friendly but depend on a device’s hardware security. OKX’s approach to multi‑layered login reduces account‑takeover risk, but it cannot eliminate phishing or social‑engineering attacks that trick users into approving session transfers.
Case scenario: logging in to check a leveraged position and move funds
Imagine you’re on the road in the US, using a public Wi‑Fi hotspot. You want to check a 5x cross‑margin position and move a portion of your spot BTC to a personal Web3 wallet. Your decision path matters:
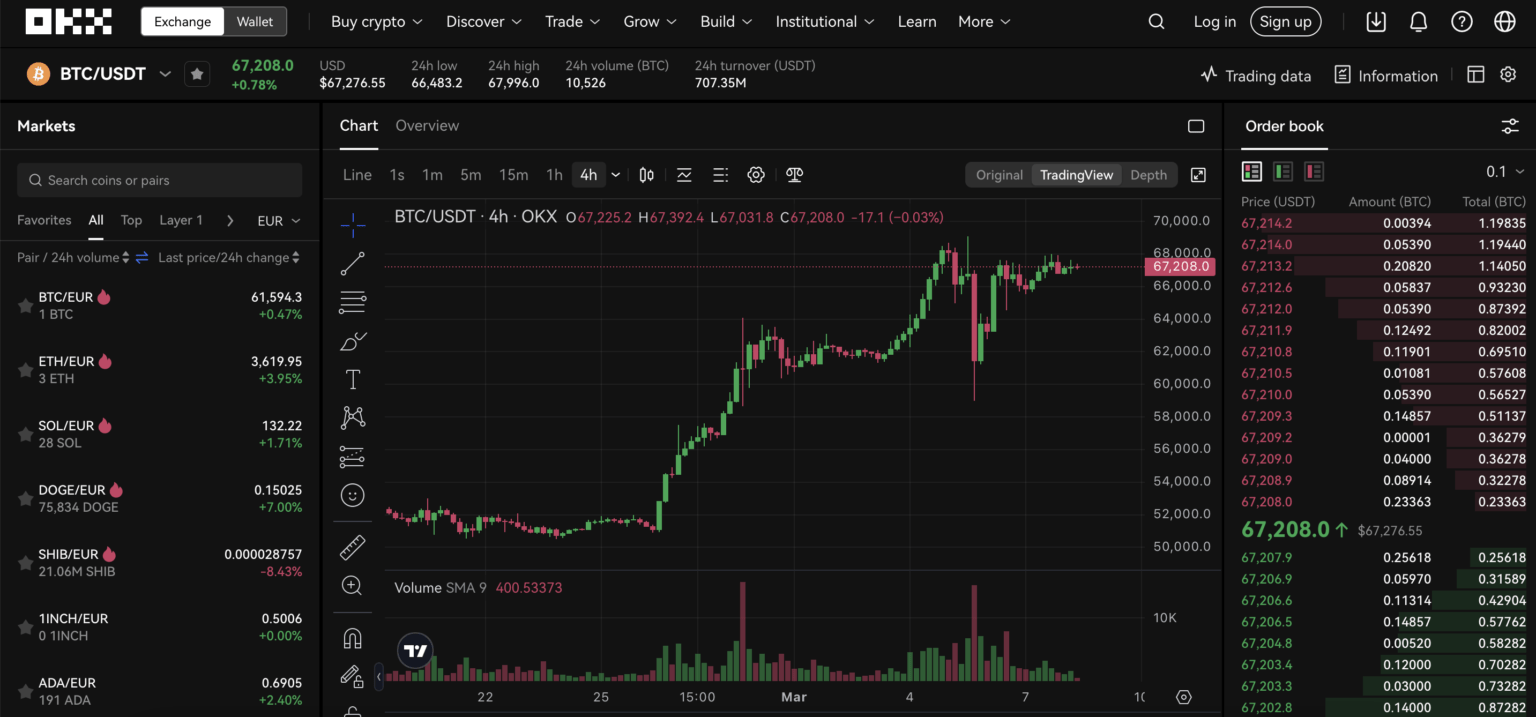
– Web login on a laptop: gives full TradingView charts and access to derivatives, but browser extensions or keyloggers on public machines pose risk. Session tokens on web can persist and be stolen if you forget to revoke them.
– Mobile app: biometric login is quick and safer on a personal device. The app reduces phishing surface because it uses device‑bound credentials and push‑style 2FA, but if the device is compromised (malicious app or jailbroken phone) that protection degrades.
– Browser extension (OKX wallet extension): excellent for Web3 DApp interaction and quick swaps via the DEX aggregator, but extensions are a different trust model — they hold keys (or connect to remote keys) and can be targeted by malicious sites that request signature approvals.
In practice a safer sequence is: use the mobile app to sign in, check positions, then transfer to your non‑custodial Web3 wallet integrated with OKX only after confirming the destination address offline and using a hardware wallet if moving large amounts.
Trade-offs: Custodial convenience vs non‑custodial control
OKX offers both centralized custody and a non‑custodial Web3 wallet. The custodial path is convenient: faster trades, integrated staking (flexible and fixed lock options, plus auto‑compounding), and the exchange stores over 95% of funds in multi‑sig cold storage. That mitigates large‑scale hacks, and Proof of Reserves enhances transparency about backing. But custodial accounts are a single failure point for phishing, exchange operational errors, or regulatory holds.
Non‑custodial wallets give you key control: hardware wallet support (Ledger, Trezor) and seed phrases that eliminate a centralized attack surface. The trade‑off is responsibility — lose the seed and access is permanently lost — and additional friction when you need to trade quickly on derivatives or use margin, since funds must be moved on‑chain and may incur gas and bridge delays. For many US traders a hybrid approach makes sense: keep active, marginable capital on the exchange while long‑term holdings and DeFi exposure live in your self‑custodial wallet.
Where the login process breaks — real limitations and failure modes
There are several concrete breaking points to watch for. First, identity verification. KYC in the US requires ID and a liveness check; if KYC fails or you travel and your ID doesn’t match regional checks, some features — especially derivatives — can be restricted. Second, account recovery. If you lose access to 2FA and the registered email or phone, recovery mixes automated checks with manual review; expect delays and potential temporary freezes.
Third, external DeFi risks. Interacting with DEX aggregators or yield farming from a Web3 wallet exposes you to smart contract exploits and bridging risks. OKX’s DEX aggregation improves swap routes and liquidity sourcing, but it cannot remove smart contract risk. Fourth, delistings: exchanges remove spot pairs (recently several smaller tokens were delisted) — if you left capital in obscure pairs you may face forced conversions at suboptimal prices or delays.
Decision framework: a simple heuristic for choosing your login path
Use this three‑step heuristic before you authenticate: 1) Intent (trade quickly vs. long‑term move), 2) Exposure (how much value is at stake), 3) Attack surface (device security and network). If intent is urgent trading and exposure is moderate, use the app with biometrics on your own device. If exposure is large and intent is long‑term storage or DeFi interaction, use a hardware wallet and the non‑custodial path. If you must use web on an unfamiliar device, enable temporary viewing only and avoid withdrawal approvals until you can re‑authenticate on a trusted device.
When transferring between custodial and non‑custodial environments, always confirm addresses offline, send a small test transfer, and allow time for on‑chain finality. For margin or derivatives, be aware that liquidation risks and slippage are time‑sensitive — logging in late during volatile markets can cost more than authentication friction.
What to watch next (signals and near‑term implications)
Monitor these signals: changes to KYC/regulatory requirements in the US (which can tighten access to derivatives), announcements about delisted pairs (affects liquidity for niche tokens), and updates to OKX’s session-management or 2FA options. A practical short list: keep backups of TOTP seeds offline, enable hardware wallet support if you interact with DeFi, and periodically audit active sessions and API keys in account settings. These actions reduce the probability of a disruptive event and shorten recovery time if one occurs.
Also watch platform notices about security upgrades and Proof of Reserves disclosures — stronger transparency reduces one category of counterparty uncertainty, but it doesn’t change user‑side threats like phishing or seed loss.
FAQ — Practical answers for common login and wallet questions
Q: Can I log in from multiple devices and keep both signed in?
A: Yes, you can, and OKX will issue separate session tokens and may show active sessions. That convenience increases attack surface: a lost or compromised device can allow session theft. Regularly review active sessions and revoke any you don’t recognize. For sensitive activities (withdrawals, margin changes), consider signing out of other devices first.
Q: If I use OKX’s Web3 wallet extension, am I still protected by the exchange’s cold storage?
A: No — the extension represents a non‑custodial model. Assets in your Web3 wallet are under your private key control and not covered by exchange custody policies or cold storage. That gives you control and responsibility. For assets you want exchange protection for, keep them in the custodial account.
Q: What is the safest 2FA option for US traders?
A: From a security perspective, an authenticator app (TOTP) combined with hardware security keys is stronger than SMS. Biometrics on a personal, up‑to‑date mobile device is convenient but depends on device integrity. The right choice balances convenience and loss‑recovery: store backup codes securely offline.
Q: Where can I find the official OKX login portal?
A: For step‑by‑step guidance on the web login flow and session tips, see this okx login resource which walks through the screens and common pitfalls: okx login
Final takeaway: the sign‑in is not merely gateway friction; it’s an operational decision point that determines custody model, exposure window, and recovery paths. Treat each authentication as a contextual trade‑off: protect large positions with hardware keys and non‑custodial wallets, use app biometrics for routine monitoring, and minimize permanent holdings on exchange for long‑term assets. That simple mental model — intent, exposure, attack surface — will sharpen your choices the next time you click “okx sign in.”
